Zero-Trust Security with AI Malware Detection
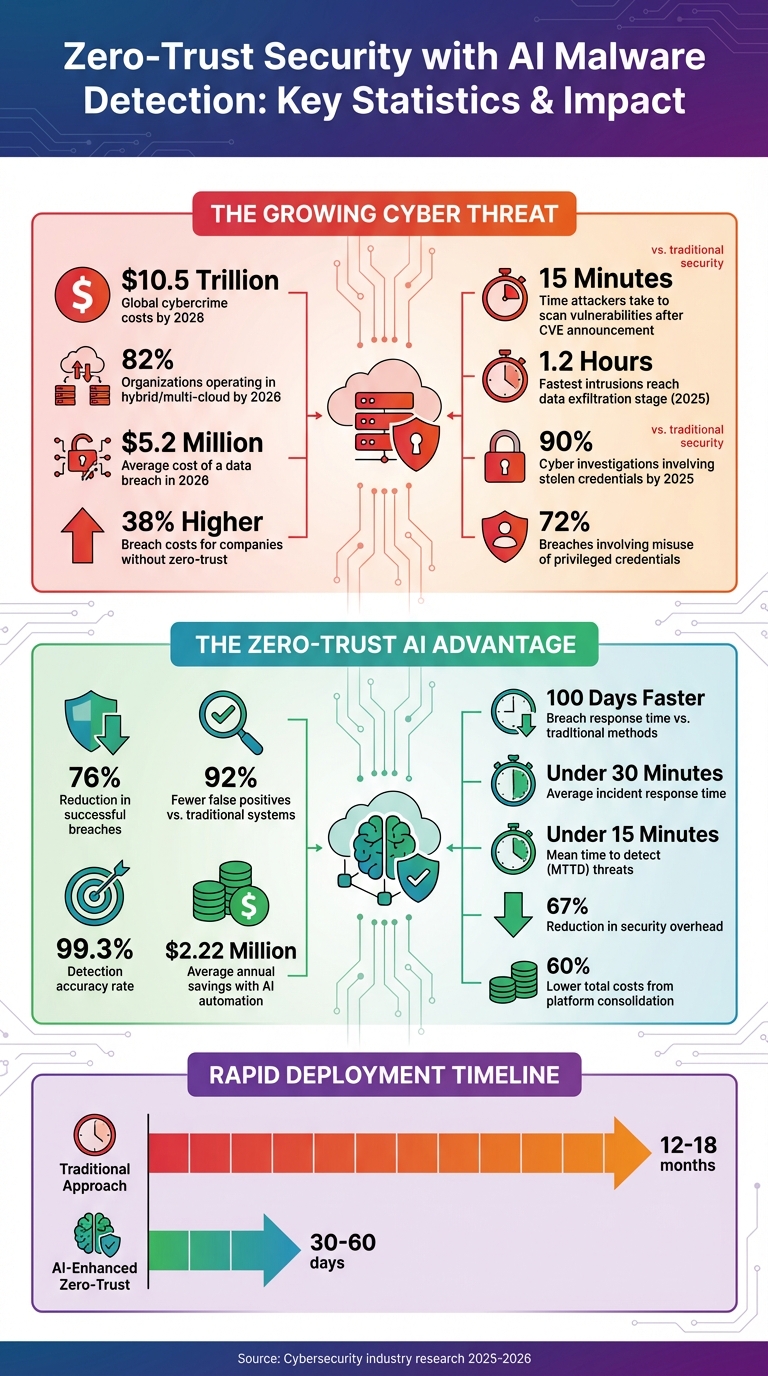
Cybersecurity has changed. With global cybercrime costs projected to hit $10.5 trillion by 2026, attackers are leveraging AI to launch faster, more advanced attacks. Traditional security models no longer work. Enter zero-trust security, which operates on the principle of "never trust, always verify" - and AI-driven malware detection is making it smarter and faster.
Here’s what you need to know:
- Zero-trust security continuously verifies every user, device, and application, reducing the success of breaches by 76%.
- AI enhances this by detecting threats in real time, cutting breach response times from days to just minutes.
- Organizations using AI-powered zero-trust systems report 92% fewer false positives and save an average of $2.22 million annually.
Why does this matter? Hybrid and multi-cloud environments are now the norm, with 82% of organizations operating in these setups by 2026. Attackers are exploiting stolen credentials and launching AI-driven attacks that evolve too quickly for traditional defenses. AI-powered zero-trust systems address these challenges by continuously monitoring, detecting, and responding to threats at machine speed.
If you’re not adopting zero-trust with AI, your risk - and costs - will only grow. The average cost of a data breach in 2026 is already $5.2 million, with costs 38% higher for companies without zero-trust protections.
Zero-Trust Security with AI: Key Statistics and Impact Metrics
AI with Zero Trust Security
sbb-itb-3b7b063
Zero-Trust Security Principles
Zero-trust security revolves around three guiding principles designed to safeguard modern cloud environments. These principles are crucial in addressing vulnerabilities that traditional security models often overlook, especially as global cybercrime costs are projected to hit $10.5 trillion by 2026.
Never Trust, Always Verify
This principle assumes that every access request could be a threat, no matter where it originates. Unlike older security models that grant trust after a single authentication, zero-trust systems continuously validate identity throughout a session. This validation relies on multiple factors, including user behavior, device health, geographic location, and time of access.
The importance of this approach is underscored by the numbers. By 2025, 90% of cyber investigations will involve attackers exploiting stolen credentials instead of bypassing firewalls. For instance, Palo Alto Networks Unit 42 highlighted a case where attackers used valid OAuth tokens to bypass authentication and infiltrate a Salesforce environment, exploiting nearly 100 unmonitored third-party integrations.
AI plays a key role in making continuous verification scalable. Using AI-driven platforms, organizations can assign real-time trust scores that dynamically adjust user privileges when unusual activity is detected. This level of automation is a core capability of AI cloud engineering platforms. This has dramatically reduced incident response times - from days to just minutes.
"The foundational principle of zero trust is simple yet powerful: 'Never trust, always verify.' Unlike traditional security models that assume internal network traffic is trustworthy, zero trust treats every access request as potentially hostile, regardless of origin."
– Anand Prasad, Security Blogger
Least Privilege Access
The principle of least privilege access ensures users only have the permissions they need to perform their tasks. This is often executed through Just-in-Time (JIT) and Just-Enough-Access (JEA) protocols, which grant temporary elevated permissions only when necessary.
This approach is critical because 72% of breaches involve the misuse of privileged credentials. By limiting access rights, organizations can significantly reduce the potential damage from a breach. In cloud environments, regular quarterly audits are essential for identifying and revoking unnecessary access permissions before they become liabilities. By adhering to this principle, organizations not only minimize risks but also enhance their ability to contain potential threats.
Assume Breach
Zero-trust systems operate under the assumption that attackers may already have infiltrated the network. Instead of focusing solely on keeping intruders out, this principle prioritizes containment and damage control through techniques such as microsegmentation and constant monitoring.
On average, attackers spend 11 days moving laterally within a network before being detected. Microsegmentation helps mitigate this risk by dividing the network into isolated zones, ensuring that a breach in one area doesn’t compromise the entire system. Each segment requires separate authentication, effectively blocking the lateral movement attackers rely on to access critical assets.
AI enhances this defense strategy by automating responses to suspicious activity. When anomalies are detected, AI tools can quarantine compromised devices and revoke access immediately - without waiting for human intervention. This rapid action is essential, as the fastest 25% of intrusions in 2025 reached the data exfiltration stage in just 1.2 hours.
"Assume breach: Operate under the assumption that attackers are already in your environment. Design your security to limit lateral movement and contain damage."
– Jim Black, Senior Product Marketing Manager, Akamai
These principles provide a strong foundation for AI-driven malware detection, which will be explored in the next section.
How AI Detects Malware
AI-driven malware detection strengthens cloud security by analyzing behavior in real time, building on the zero-trust principle of continuous verification.
Unlike traditional antivirus software that depends on databases of known threats, AI focuses on behavioral patterns. This shift is essential because modern malware evolves quickly to avoid detection methods based on static signatures. Behavioral analysis allows AI to spot these threats more effectively.
AI uses three main techniques to detect and stop malware: establishing baselines, predictive threat modeling, and continuous network monitoring. These methods allow organizations to respond to threats faster and more efficiently. In fact, companies using AI and automation for security save an average of $2.22 million annually and reduce breach response times by nearly 100 days compared to those relying on traditional approaches [14,15].
Behavioral Analysis and Anomaly Detection
AI systems continuously monitor activity to identify anomalies. They start by learning what "normal" behavior looks like in your cloud environment - tracking login times, geographic locations, data access patterns, and application usage. Once a baseline is set, deviations such as unusual CPU spikes, large file transfers to unknown IPs, or unauthorized encryption attempts are flagged immediately [14,15].
This approach, called heuristic analysis, focuses on how code behaves rather than just its structure. Advanced systems combine static analysis (examining code structure) with dynamic analysis (observing code execution) to provide insights into a file's intent [13,15].
A striking example comes from May 2025, when Palo Alto Networks' machine learning team identified a malicious file that had been wrongly marked as "benign" by 94% of VirusTotal vendors for two years. The AI flagged the file by analyzing its behavior, including downloading encrypted shellcode, using an invalid PE checksum, and showing signs of packing. After a rescan prompted by these findings, the file was correctly classified as "malicious" and identified as Cobalt Strike.
"The fundamental question is no longer if a file is malicious, but how it is malicious."
– Pamela Toman, AI Research, Palo Alto Networks
AI also handles 51% of the 22,000 weekly security alerts most organizations face, without requiring human input. When an anomaly is detected, AI can isolate affected systems, block malicious IPs, or enforce multi-factor authentication - all in real time, minimizing the threat's impact.
Predictive Threat Modeling
Predictive threat modeling helps anticipate and prevent attacks before they occur. Machine learning algorithms analyze historical attack patterns and external threat intelligence to forecast which attack vectors are most likely to target your systems.
This capability is critical because attackers are moving faster than ever. In 2025, the fastest 25% of cyber intrusions reached the data exfiltration stage in just 1.2 hours, down from 4.8 hours the previous year. Additionally, attackers begin scanning for vulnerabilities within 15 minutes of a CVE announcement. Predictive AI helps defenders stay ahead by identifying potential vulnerabilities and lateral movement paths before attackers can exploit them [8,14].
These systems also enable dynamic security measures, adjusting access controls and policies based on the predicted risk level. For instance, if an account shows signs of credential compromise, the AI can require additional authentication or restrict sensitive data access immediately.
| Feature | Traditional Detection | Predictive AI Modeling |
|---|---|---|
| Methodology | Signature-based; known patterns | Behavioral and anomaly-based; machine learning |
| Timing | Reactive; responds after threat identified | Proactive; anticipates threats before impact |
| Threat Scope | Effective against known malware | Detects unknown, zero-day, and evolving threats |
| Adaptability | Static rules and manual updates | Continuous learning and real-time adaptation |
"AI represents a generational shift for cybersecurity, enabling smarter, faster, and more adaptive defenses against evolving threats."
– Zscaler
By combining predictive modeling with real-time monitoring, AI offers a comprehensive defense strategy.
Real-Time Network Traffic Analysis
AI keeps a constant watch on network traffic, analyzing it in real time for malware signatures and unusual patterns that could indicate a breach. Traditional tools often process traffic in batches, but AI systems work on massive datasets from network logs and endpoints instantly, catching threats that older methods might overlook.
This speed is critical as attackers increasingly use AI to scale their operations. In a simulated AI-assisted attack, the time-to-exfiltration was reduced to just 25 minutes. To counter this, defenders need AI systems that operate at the same machine speed.
AI also tracks behavioral biometrics to detect compromised credentials or insider threats. For example, it can identify if a previously trusted third-party app is now compromised by analyzing changes in its API calls or data access requests [15,16].
"AI brings speed, pattern recognition, and endurance... it runs real-time analysis 24/7."
– Rainier Gracial, Global Solutions Engineer, Spin.AI
When suspicious activity is detected, AI can immediately isolate infected systems, block malicious IPs, or require additional authentication. This rapid response is essential for combating modern polymorphic malware, which constantly changes its code to evade detection. AI's ability to adapt and respond in real time ensures that defenses remain effective against these evolving threats [14,15].
Combining AI Malware Detection with Zero-Trust Security
AI-powered malware detection brings zero-trust principles to life across vast networks of users, devices, and workloads. While zero-trust emphasizes "never trust, always verify", AI delivers the speed and intelligence needed to enforce this philosophy continuously.
This collaboration replaces static, one-time authentication with dynamic trust scoring. AI constantly evaluates trust levels based on behavior, location, and access patterns. For instance, if someone typically working within HR systems suddenly attempts to download engineering files at 3 a.m. from a new location, their trust score drops instantly. This triggers additional authentication steps or even denies access outright.
AI supports key zero-trust principles by:
- Establishing behavioral baselines for every user and instantly flagging anomalies, reinforcing "never trust, always verify."
- Automating least privilege access policies through machine learning, cutting down on the manual effort of managing permissions.
- Tracking network communications to detect lateral movements, isolating compromised systems before attackers reach sensitive data.
"Zero Trust demands continuous validation for every user, device, browser extension, and app, every single time. This approach is complemented by AI in security... AI detects anomalies and Zero Trust acts on them."
– Rainier Gracial, Global Solutions Engineer, Spin.AI
By 2026, organizations using this combined approach saw 76% fewer successful breaches and reduced response times from days to mere minutes.
Continuous Monitoring and Automated Response
Continuous monitoring ensures constant vigilance, shifting security from periodic checks to real-time validation. AI evaluates every access request, connection, and data transfer throughout a session - not just at login.
When threats arise, automated responses kick in immediately. AI-driven systems isolate compromised devices, revoke credentials, and initiate multi-factor authentication without waiting for human intervention. This rapid response is critical - organizations using AI-enhanced security can contain breaches nearly 100 days faster than those relying on manual processes, with an average response time of under 30 minutes.
One standout example is the ZenGuard framework. In live testing during 2025, it achieved a response time of under 10 seconds for threats like privilege escalation and lateral movement. It used Isolation Forest machine learning models to revoke sessions and quarantine devices automatically.
Continuous Controls Monitoring (CCM) adds another layer of automation. CCM runs scheduled checks against policy-as-code, automatically fixing low-risk issues like publicly accessible cloud storage or missing MFA policies. This reduces exposure windows from days to mere minutes.
| Metric | Traditional Security | Zero Trust AI |
|---|---|---|
| Mean Time to Detect (MTTD) | 207 days | < 15 minutes |
| Breach Prevention Rate | Varies | 98%+ |
| False Positive Reduction | Baseline | 85% - 92% |
| Admin Overhead | High (Manual) | 67% Reduction |
| Response Time | Days | < 30 minutes |
Improving Verification with Behavioral Analytics
Behavioral analytics enhances trust scoring by identifying what "normal" looks like for every user, device, and service account. User and Entity Behavior Analytics (UEBA) flags deviations from these baselines.
This approach is especially effective against polymorphic malware, which alters its code to evade detection. AI counters this by analyzing behavioral patterns like unusual file activity, rogue scripts, or abnormal data flows. Even brand-new malware reveals its presence through its actions.
Verification becomes adaptive. For example, a user accessing routine systems during business hours from their office maintains a high trust score and experiences no interruptions. However, accessing sensitive data at 3 a.m. from a new country triggers immediate security measures - such as multi-factor authentication or alerts to the security team.
SpinOne's AI Risk Assessment platform showcases this in action. It monitors over 400,000 apps and browser extensions in real time, blocking those that request excessive permissions. This addresses the shadow IT problem, which contributes to security incidents in 85% of organizations.
Machine identities, such as service accounts and API keys, also benefit from AI. A study of 680,000 cloud identities revealed that 99% had excessive permissions, often unused for months. AI identifies these over-privileged accounts and adjusts permissions to match actual usage, closing a critical security gap.
"AI transforms an otherwise complex, resource-intensive, multi-year initiative into a rapidly deployable and operationally scalable security strategy."
– Umesh Mahajan, VMware
Protecting Endpoints
Endpoints - like laptops, mobile devices, servers, and IoT devices - are frequent targets for attackers. In 2025, identity-based techniques accounted for 65% of initial breaches, highlighting the importance of endpoint security in zero-trust strategies.
AI fortifies endpoints by monitoring device health, application behavior, and network connections. If a device exhibits signs of compromise - such as abnormal CPU usage, unauthorized encryption attempts, or suspicious outbound connections - AI isolates it from the network, blocks malicious IPs, and enforces additional authentication.
Preventing lateral movement is equally critical. Attackers often use compromised endpoints to access more valuable systems. AI maps communication patterns to detect unauthorized "east-west" traffic and misconfigurations. VMware's vDefend platform, for example, uses this method to secure applications and shorten zero-trust implementation timelines from months to weeks.
Emerging autonomous AI agents present new challenges. These systems need strict guardrails to prevent misuse. AI-based intent detectors monitor interactions with internal AI systems, flagging sensitive queries or unauthorized data access attempts.
Phishing-resistant MFA is another essential component. Traditional MFA can be bypassed using advanced techniques like session hijacking or deepfakes. Hardware-based solutions like FIDO2/WebAuthn provide cryptographic verification, countering these advanced threats.
Automated patching further strengthens endpoint defenses. Attackers often exploit newly announced vulnerabilities within minutes of disclosure. AI-driven patch management identifies exposed assets and applies critical updates automatically, closing this exploitation window.
Cloud platforms also benefit from these AI-driven defenses. Solutions like Kanu AI simplify the enforcement of zero-trust measures across complex infrastructures.
Benefits and Challenges of AI in Zero-Trust Security
Benefits of AI in Zero-Trust Security
AI has transformed zero-trust security into a practical and scalable defense strategy. Companies using AI-driven zero-trust systems reported 76% fewer successful breaches and slashed incident response times to under 30 minutes. These systems also achieved an impressive 99.3% detection accuracy, alongside a 92% reduction in false positives compared to traditional SIEMs.
One of AI's biggest advantages is speed. It operates at machine speed, isolating compromised devices and revoking credentials in real-time. This reduces detection times significantly, making it harder for attackers to exploit vulnerabilities. Additionally, AI has drastically cut intrusion exfiltration times, limiting the damage caused by breaches.
Automation plays a crucial role here. Automated policy enforcement has reduced security overhead by 67%, allowing teams to focus on more strategic tasks. Implementation timelines that once stretched to 12–18 months have been shortened to just 30–60 days, and consolidating multiple tools into unified AI-powered platforms has lowered total costs by 60%.
AI's behavioral analytics bring another layer of protection. By establishing baselines for every user and device, AI can detect subtle warning signs like lateral movement or credential theft - threats that signature-based tools often miss. This predictive capability is especially vital, given that 99% of cloud identities have excessive permissions, creating opportunities for attackers.
Despite these advancements, integrating AI into zero-trust frameworks comes with its own set of challenges.
Challenges and Solutions
While AI-enhanced zero-trust security offers clear advantages, it also introduces new risks that require careful management. Adversarial attacks are a prime example. Techniques like data poisoning corrupt AI training datasets, making malicious software appear benign, while evasion attacks tweak malware just enough to bypass detection . A high-profile example occurred in September 2023, when MGM Resorts International suffered $110 million in losses after attackers used AI to clone an employee's voice, tricking the help desk into resetting credentials.
Model integrity is another concern. Attackers can use model inversion to extract sensitive data from AI outputs or conduct extraction attacks to steal proprietary AI models through repeated API queries . In 2023, Samsung faced this issue when employees inadvertently uploaded proprietary source code to ChatGPT, prompting the company to temporarily ban generative AI tools.
"All antiviruses suck when adversaries are generating malware with AI - because every sample is new, always one step ahead of traditional defenses."
– Danny Jenkins, CEO and Co-founder, ThreatLocker
Another challenge is concept drift, where AI systems lose accuracy as attack patterns evolve and production data diverges from training datasets. For instance, Zillow's "Zillow Offers" program collapsed in 2021 after concept drift caused its pricing models to fail, resulting in losses exceeding $500 million. Regular retraining with up-to-date threat intelligence can mitigate this issue .
Shadow AI is a growing problem, as unapproved tools create unmonitored pathways for potential data breaches. A striking 78% of knowledge workers admit to using unauthorized AI tools, yet only 32% of organizations have policies in place to address this. To counter this, application allowlisting ensures that only approved tools can run, while sandboxing isolates AI agents in temporary environments where credentials expire after specific tasks .
Finally, the opaque or "black box" nature of AI complicates compliance and troubleshooting. Security teams often struggle to explain why AI systems make certain decisions. To address this, maintaining detailed data lineage and using Software Bills of Materials (SBOMs) for AI models can help trace every component back to its source, ensuring only thoroughly vetted models are deployed.
How to Implement AI Malware Detection
Conduct a Security Audit
Start by identifying what needs protection. Create a detailed inventory of all AI assets, including models, datasets, machine learning pipelines, and API endpoints. Classify these assets based on their sensitivity and how critical they are to your business operations. This process will help you pinpoint the most vulnerable areas and decide where to focus your defenses first.
Rather than trying to overhaul everything at once - a move that often leads to failure and resistance - prioritize high-risk areas. Once you've mapped out your assets, the next step is to deploy AI-driven security tools that work seamlessly within your cloud environment.
Deploy AI-Powered Security Tools
With a clear understanding of what requires protection, introduce AI-powered tools like SIEM (Security Information and Event Management) and UEBA (User and Entity Behavior Analytics) systems. These tools excel at real-time threat detection by processing enormous amounts of data. For instance, Zscaler's Zero Trust Exchange processes over 500 trillion signals daily to enforce security policies.
Opt for tools that integrate smoothly with your existing cloud setup to minimize management headaches. Solutions such as AWS GuardDuty and VMware vDefend simplify operations by eliminating the need to manage multiple APIs or operating systems. Additionally, implement identity-focused controls that evaluate authentication based on factors like device health, user location, and historical behavior patterns. This approach can significantly reduce the mean time to detect (MTTD) threats, often bringing it down to under 15 minutes.
Automate Policy Enforcement
After setting up your AI tools, automate policy enforcement to maintain consistent protection. Configure systems to apply Just-in-Time (JIT) and Just-Enough-Access (JEA) principles, ensuring users and AI agents only have the permissions they need for specific tasks. When anomalies are detected, automate the response - whether that means isolating the threat, revoking access, or triggering an incident response protocol.
Organizations that leverage AI and automation for preventive security measures report average savings of $2.22 million annually. Use AI to amplify your security efforts but maintain human oversight for critical actions. For example, enable automated approvals for low-risk, routine tasks while requiring human approval for high-stakes operations affecting production systems. Regularly update your AI models with the latest threat intelligence to counteract evolving malware and avoid issues like model drift.
Conclusion
The cybersecurity world is evolving at breakneck speed. Attackers are now leveraging AI to identify vulnerabilities within minutes - just 15 minutes after disclosure, to be exact - and can exfiltrate data in as little as 1.2 hours. In this high-stakes environment, conventional defense methods simply don’t cut it anymore. The combination of zero-trust security and AI-driven malware detection has proven to be a game-changer, reducing successful breaches by 76% and saving organizations an average of $1.9 million per breach.
"The cybersecurity paradigm has fundamentally shifted. Perimeter-based security models cannot protect organizations operating in distributed, cloud-centric environments." – Seceon Inc
By integrating zero-trust principles with AI capabilities, organizations can establish a proactive defense system. This system continuously verifies access requests and identifies threats at machine speed. With predictions indicating that 75% of breaches in 2026 will involve compromised identities using legitimate credentials, identity-focused controls paired with behavioral analytics are becoming non-negotiable. AI enhances zero-trust strategies by automating verification processes, enabling just-in-time access, and spotting anomalies that hint at lateral movement before attackers can strike critical assets.
To implement these strategies effectively, organizations should take a phased approach. Start by addressing the highest-risk areas: deploy phishing-resistant multi-factor authentication for sensitive roles, automate policy enforcement for repetitive tasks, and unify security platforms to minimize alert fatigue. With the average cost of a data breach projected to hit $5.2 million in 2026, and costs rising by 38% for companies lacking zero-trust measures, the question isn’t whether to adopt AI-enhanced zero-trust security - it’s how quickly you can make it happen.
For organizations navigating cloud-based environments, platforms like Kanu AI (https://getkanu.com) offer tools to simplify the transition to AI-augmented zero-trust architectures. These platforms combine rapid deployment with strong security measures, ensuring seamless operations alongside fortified defenses.
FAQs
How does AI malware detection work without signatures?
AI-driven malware detection steps up the game by spotting threats without relying on traditional signatures. Instead, it uses advanced neural networks and machine learning models to analyze how code behaves, identify patterns, and flag anomalies in real time. This means it can catch zero-day and fileless threats - types that often slip past older, signature-based methods. By focusing on behavior rather than predefined signatures, this approach offers a smarter, more adaptable way to strengthen security.
What’s the fastest way to start zero trust with AI in the cloud?
The fastest way to roll out zero-trust in the cloud with AI is to focus on an identity-centered security framework. This approach constantly verifies and monitors every interaction. Leverage AI-powered tools to automate the verification process, enforce security policies, and deliver real-time insights, which speeds up implementation. To make it effective, ensure granular access controls, robust data encryption, and continuous monitoring across cloud systems. These steps help create scalable zero-trust practices supported by ongoing validation.
How do you reduce AI security false positives without missing threats?
Reducing false positives in AI security relies on filtering systems that can tell the difference between routine activities and actual threats. Machine learning plays a key role here, as it processes contextual data, identifies patterns, and adjusts in real-time to cut down on unnecessary alerts. When combined with zero-trust security - an approach that focuses on strict identity verification and ongoing checks - AI becomes even more precise. This integration ensures that real threats are detected while keeping false alarms to a minimum.
